In a perfect world common sense and a solid work ethic would keep employees on task throughout the day, but the world we live in is full of online distractions.
Personal email, games and social media are all elements contributing to a slump in workplace productivity.
A 2010, Salary.com survey indicates that on average, around 64% of workers wasting one hour or less each day at work, while 14% waste 3 or more hours each workday (48% of this time is spent surfing the web which I’m sure isn’t surprising).
Once thought of as draconian or needlessly complex, the implementation of computer usage policies (often coupled with monitoring) is on the rise. The American Management Association, suggests that up to 45% of employers tracking content, keystrokes, and time spent at the keyboard (2008). Interestingly though, more than half of all businesses do not have social media and networking policies in place despite the fact that 76 percent use social networking for business purposes (Proskauer). By all accounts, there’s a massive divide – both in the way Internet monitoring is considered, and the way it is commonly policed.
There is an obvious need to computer and network usage in the workplace; an effective computer and network usage policy, with the assistance of sensible monitoring tools can help address a number of real problems that are costing businesses thousands of dollars in lost productivity every day.
Reasons to monitor
Employees are paid for their time at work, so it’s natural to want them to use that time to complete work activities. Yet nearly half the employees in a study by Nucleus Research admitted to accessing Facebook during work hours, with 87 percent of those not able give a work-related reason for their use. Businesses of all shapes and sizes have been caught off guard by Facebook, Twitter and social gaming – an obvious reason to consider an Internet or Computer usage policy, but there are many others…
Piracy and security issues
Monitoring employees’ computer use can be an effective tool in preventing software piracy at work. While it may not be the first reason most employers choose to monitor, businesses are responsible if their employees to use unlicensed software, even without management’s knowledge. As Kane Bennett outlines, “Civil penalties include monetary damages for the software publisher’s lost profits and statutory damages up to $150,000 for copyright infringement.” Costs can go even higher in the even criminal charges are filed.
Piracy also often introduces infrastructure and security concerns. The sites used for software and media piracy often leave visitors with malware, viruses and spyware, which can compromise private business data and affect the proper functioning of your machines If employees downloading large files, bandwidth can quickly become a concern. Even frequent small downloads can raise issues. A study by the International Information Management Association described bandwidth problems resulting from employees having real-time data, such as news reports or stock data, sent to their desktop. The employer in this situation encountered an unexpected double-digit loss of bandwidth.
Computer & network misuse
Illegal downloads and other peer to peer activities should be addressed in a computer usage policy. Peer-to-Peer technologies can be used to download illegal files, including copyright protected material which is punishable under various federal laws. They can also be used for completely legitimate purposes, but does that mean you would want people doing this on your time at work?
One example – in a recent interview on Motherboard.tv, an anonymous school IT Director described how he is using his schools computer network to mine Bitcoins – he points out what he’s doing is legal, “I am pretty sure that’s a grey area. I’d be I am pretty sure my employers wouldn’t be thrilled if they found it though”. Bitcoin mining is just one example of ways that computer equipment can be misappropriated in the workplace – if there’s no policy for this type of use, then there is often no grounds for retribution, or dismissal.
Efficiency metrics
An effective computer usage policy shouldn’t just be a way to protect your hide, or the grounds to punish workers who break the terms of and agreement. A water tight usage policy should let your staff know when and how their time at the computer is being monitored.
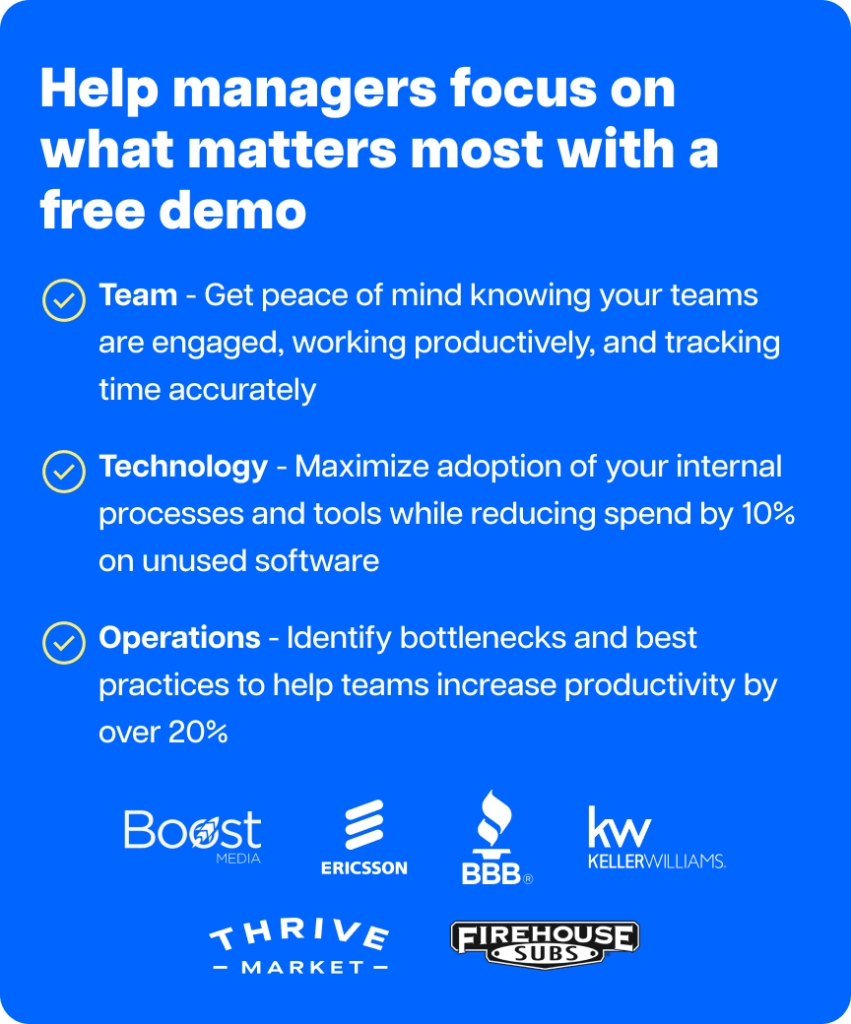
Some monitoring solutions allow you to block areas of the web, which can come in handy if you discover employees spending lots of time on social networks or other sites. Others offer web usage timers, which allow employees to use the Internet for personal purposes at select times, such as during lunch breaks. Popular solutions for network monitoring include OpenDNS, and Nagios, while many business prefer to use complete time tracking solutions like Time Doctor or Staff Cop, which has a screen monitoring software, application and Internet usage, only during work hours. This sort of software has the added benefit of being usable by telecommuters or contractors who worked at fixed hourly rate outside of an office environment (including private or fire walled networks).
If you’re monitoring how employees use their computers at work, you can also study those results to learn more about efficiency. Most monitoring software packages include analytic tools. You may find that certain websites are distracting employees from their work, and decide to block them or record their use. You may find some employees using online tools that allow them to get more done, and decided to share those tools with the rest of your workforce. Some monitoring programs automatically track the time employees spend on each work task, giving you a clearer picture of the workflow and any potential snags.
Another way monitoring your employees’ computer use can benefit you is in measuring personnel performance. Having this data on hand will make it easy to quantify performance in an objective way and give raises and incentives accordingly. You’ll be better able to identify top performers, and have a tangible record of time wasted by under-performers.
Privacy laws and monitoring rights
Shawn E. Tuma , a technology and litigation attorney in Plano, Texas, said while many employees feel they have special rights when using a computer in the workplace, that is simply not true.
“A computer with internet and email access is an asset that is owned by the employer and is provided as a tool to assist the employee in doing his or her job,” Tuma said. “Having a computer use policy is a great way to emphasize and reinforce to the employee that the computer is a business tool and should be used in that manner.”
An employer’s right to monitor employee computer use is granted by three exceptions to the Electronic Communications Privacy Act of 1986. The first, called the business exception, gives employers the right to intercept communication on qualified devices during the course of business. The second, the consent exception, allows employers to monitor communication as long as at least one individual gives their consent. And third, the service provider exception lets employers access information stored on wire or electronic communication systems they provide, such as email or voicemail, to protect their property rights.
These exceptions make it possible for employers to use a variety of monitoring systems and methods. They can use software that allows them to see data stored on company computers or displayed on the screen, whether the computer is being used in the workplace or at another location. They can track the amount of time employees spend working as well as the time they remain idle. If employees’ work requires heavy word processing or data entry, employers can also monitor their keystrokes.
Tuma said, “Generally, because the workplace computer is owned by the employer, the employee has no reasonable expectation of privacy with regard to anything he or she does with that computer.”
There are, however, some limitations to employers’ monitoring rights. For example, union contracts may have stipulations that prevent monitoring. The state of California has some constitutional privacy protections that may come into play.
However, in the case of Holmes v. Petrovich Development Company, LLC the California Court of Appeals found that because a monitoring policy had been explicitly stated, the employee in question had no expectation of privacy. This meant the employer could legally monitor her email communication, even superseding the right to attorney-client privilege. On the other hand, the New Jersey Supreme Court maintained an employee’s right to attorney-client privilege when using a personal email account protected with a password in Stengart v. Loving Care Agency.
Since privacy law can be somewhat ambiguous depending on your jurisdiction and specific scenario, it’s important to construct a watertight computer use policy. Recently, Tuma said, courts have looked to employers’ policies to determine whether the employer had formalized limits in place when mediating such workplace disputes.
Does your company need a written social media usage policy?
With the social media landscape in overdrive, social media policies, as important as they are, are often an afterthought, or are shelved for more important or timely considerations… although some recent cases have meant that companies are taking the idea more seriously. The Internet is permanent, and workers (particularly in media or marketing industries) need to be responsible for their posts. When in doubt, do not post is a useful idiom.
Marketing Sherpa (A popular integrated marketing journal) also stresses the importance of good social media policy, which will “encourage employees to take part in promoting their brand online, while serving as a safeguard against tarnishing the organization’s reputation, or exposing proprietary assets”. As mentioned before, only 25% of organizations have written and implemented a social media policy (and typically in larger organizations).
As Marketing Sherpa points out “This is a double-edged sword because larger organizations are also more likely to have legal departments, and as such, draft a social media policy that may impede sharing any type of information, which could discourage employee participation”. Without social media policies, employees have no insight or information about what they’re allowed to do, but there’s no need to completely disarm you companies social media channels.
Shawn Tuma notes that a frequent pitfall for employers is when policies prohibit employees from saying negative things about the company on social media sites. “The policy isn’t necessarily the problem, it’s when the employer tries to enforce it by making an employment decision based upon that violation of the policy,” he said. “In several cases it has been found that the employer improperly terminated the employee for engaging in protected speech-like activities.” Tuma said if an employer is considering such a policy, they should consult an attorney, because rules can vary based on location and circumstances.
Points your internet usage policy should absolutely cover
- While you want your policy to be specific in many areas, you’ll want to include a blanket statement saying all aspects of employee use of company-owned equipment can be monitored at any time and without notice. This terminology will make it clear that employees have no expectation of privacy when it comes to using employer equipment.
- Stating the reasons for the policy helps make sure employees don’t feel their right to privacy is being needlessly infringed. There are many reasons to monitor employee computer use, as discussed earlier in this article. Mention some of them in your policy.
- Describing what constitutes improper use of employer-owned equipment is vital. As, Shawn Tuma mentions, ” the threshold in determining whether an employee has violated the Computer Fraud and Abuse Act is determining whether they exceeded authorized access of the employer’s computer, or accessed it without authorization”. He recommends that policies “include language that clearly defines and limits the employees’ authorization to access the computer, use of information accessed or obtained from the computer, and that [also] terminates the employees’ authorization to access the computer if he or she does so in violation of the policies.”
- Be sure to also include a description of proper employee computer use in your policy. If your employees use social media to interact with their customers, this activity will need to be described and differentiated from improper use of the same social media sites. Tuma stresses the importance of “tailoring the policy to the nature of the employer’s business, the employee’s duties … and what levels of authorization and freedom they may require in order to perform their job.”
- Your policy should prohibit unauthorized encryption of information such as email on business computers, such as with solutions like PGP. There is no clear rule about employer access of password-protected employee accounts, and some courts have prohibited employers from accessing them.
- To make it possible to enforce your computer use policy, state that violating the policy can lead to disciplinary action, and be specific. Describe whether warnings are required before action is taken, and what the action may consist of.
- Add a zero-tolerance policy for communication that is offensive, discriminatory, or constitutes harassment. Even if an employer is unaware of illegal activity, they may still be held responsible for their actions. As Tim New states, “Having the ability to regulate computer use and not addressing it could open the company to liability for sexual harassment and hostile workplace environments.”
Implementing a computer use policy
New, the managing partner of Kansas City-based Onsite Logic, helps small business clients implement computer use policies and monitoring. He said, “In general, most employers feel the computer should be used for business purposes. However, most don’t have any issue with someone receiving an occasional email from their kids’ school or checking a website to find a phone number or order lunch. The challenge is in explaining where the line is between occasional personal use and chronic abuse.”
Once you’ve drafted a computer use policy, have each employee read and sign a copy. Keep this copy in the employee’s file. Update the policy at least yearly, communicate the updates to employees, and have them sign an acknowledgement. New said, “This type of policy is best implemented when it is not a legal document placed on a shelf and pulled out to punish an individual when they cross a line. It is best implemented when it is an ongoing method of communication, recognizing that it will change as the tools change.”
Provide copies of the computer use policy to employees in writing. Also include it in welcome manuals or codes of conduct.
In order to be effective, the policy must be applied to all levels of the organization, and it must be enforced. New thinks “many business owners shy away from monitoring because it can seem too heavy-handed for the culture they want to create. However, a policy without enforcement is not a policy.”
In conclusion
In addition to protecting an employer from potential pitfalls, a comprehensive computer use policy functions as a communication tool to employees. A good policy should make it clear exactly what’s acceptable – and what isn’t – when it comes to computer use. If you don’t like the idea of issuing a rigid set of rules, think of it as a starting point for an ongoing dialog about how your business will be run.
Regardless of future changes, you will need a practical and legally sound basis to build from.

Rob Rawson is a co-founder of Time Doctor which is software to improve work productivity and help keep track of what your team is working on, even when working remotely.